|
Introduction | 3B Description | ABY Changes | Schematics | Boost Control | Diagnostics Bosch Motronic Info |
|
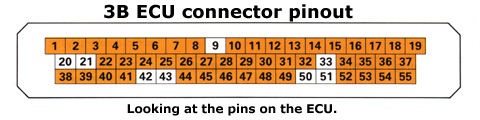
Motronic ECU Pinout for the 3B Engine IMPORTANT - The information on this page is ONLY applicable to the 3B engine. It is NOT transferable to the ABY engine. The image below depicts the pin locations as if viewing the connector on the ECU.
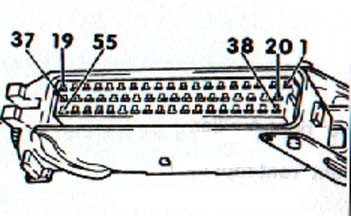
The image below depicts the 3B ECU pinout when viewing the cable assembly.
The following table defines the functionality of each of the 55 pins on the 3B Motronic ECU. Revolut: DesktopAuthor: [Generated for Academic Review] Date: April 14, 2026 Abstract Revolut, a leading global neobank, has traditionally operated under a "mobile-first" paradigm, offering its full suite of banking, trading, and cryptocurrency services exclusively via smartphone applications. As the company matures from a fintech challenger into a comprehensive financial ecosystem, the absence of a dedicated desktop interface (web or native application) represents a growing operational and strategic limitation. This paper analyzes the technical feasibility, user demand, security implications, and competitive positioning of a Revolut Desktop platform. It concludes that while mobile remains primary, a hybrid desktop offering is essential for capturing high-net-worth individuals, professional traders, and business clients, provided Revolut can address cross-device synchronization and advanced threat vectors. 1. Introduction The fintech landscape has evolved significantly since Revolut’s founding in 2015. Initially, mobile-only models disrupted traditional banking by reducing overhead and offering real-time notifications. However, competitors like Monzo (limited web access), N26 (full web interface), and traditional brokers (e.g., Interactive Brokers, TradingView) have proven that serious financial activities—such as multi-chart technical analysis, bulk transaction reconciliation, and tax reporting—are inefficient on a 6-inch screen. | Threat | Mobile | Desktop | Mitigation Strategy | | :--- | :--- | :--- | :--- | | Phishing | Lower (app-based) | Higher (fake websites) | Mandatory hardware token/U2F key for desktop login | | Keylogging | Rare | Possible | On-screen PIN pad for sensitive actions | | Session hijacking | Biometric bound | Cookie-based | Short-lived JWTs + device fingerprinting | | Malware | Sandboxed | OS-level | Require OS security checks (e.g., TPM 2.0) | revolut desktop |
Last Updated 12th May 2002